In July of this year, China’s first regiment of S-400 surface-to-air missile (SAM) systems was delivered by Russia and accepted into PLA service. The following month, Russia confirmed that the last 10 Su-35s of an order for 24 would arrive by the end of 2018. The deals were originally signed, respectively, in 2015 and 2014, with S-400 negotiations having started as far back as 2011.
Now, some months later, the United States has decided that sanctions are the appropriate tool to “punish” China for violating other sanctions against Russian entities including Rosboronexport, under the 2017 “Countering America’s Adversaries Through Sanctions Act” (CAATSA). The Chinese CMC’s Equipment Development Department and its chief will be barred from conducting financial transactions in the United States.
Beijing, naturally, has no intention of putting an end to its weapons purchases from Moscow.
But leaving aside the inexplicable timing (and apparent ex post facto application) of such a decision, it would seem foolish on its face. Not only is the interstate arms trade something that the United States – given its position as the world’s largest arms dealer – would seem to want to leave relatively unregulated, but to try and interfere in a commerce arrangement between two Great Powers has historically not ended well for the interloper. Imposing CAATSA-related sanctions also ignores the existing Western arms embargo against China, dating back to the Tiananmen Square massacre, and which Beijing has managed to circumvent for years through various financial mechanisms and yuan-denominated transactions. Sanctions must be a limited tool in order to have effect, and applying them in this way further weakens their utility.
The possible Chinese and/or Russian countermoves are numerous: sanctions of their own against big US (and multinational) defense contractors; pricing their own arms as “loss leaders” to displace US primacy in various markets, particularly Southeast Asia and Eastern Europe; economic punishment of US client regimes (e.g., the UAE, South Korea, Egypt), etc. In fact, the latter can already be seen with China’s immediate critical reaction to the US sale of F-16 fighter equipment to Taiwan. The sale is hardly news—and consists mostly of sustainment material for existing platforms that were previously themselves protested—but the Chinese response represents the first step in an emerging economic counteroffensive; a second front in the ongoing trade wars.
Now, you might ask, might this not just be cutting off the nose to spite the face? After all, if China financially punishes Saudi Arabia or Turkey for buying American weapons, they make it so much less likely that those nations would consider turning to Chinese or Russian imports in the future. But arms sales themselves are more than purely transactional; they are potential tools of statecraft. Look at India’s attempt to “balance” between the United States and Russia: a few P-8Is and F-16s here, a few batteries of S-400s there (the latter, however, requiring a CAATSA waiver, which has so far been promised by the Pentagon but has yet to appear). Rarely does capability alone factor into a major international arms deal; see the long list of US arms deals facilitated by the Defense Security Cooperation Agency for an idea of their importance to Washington. When capabilities are the overriding reason to obtain a system, it can have geopolitical implications of its own – see Turkey’s ongoing acquisition of the S-400 for an example of exceeding the unwritten rules of acquisition.
Not only has a CAATSA waiver failed to materialize for India’s S-400s, but so too is there nothing resembling an exception to reimposed US sanctions on Iran, following the abandonment of JCPOA. This has had the potential of threatening Indian access to and “special privileges” at the Iranian port at Chah Bahar should India seek to replace its imports of Iranian oil (Chah Bahar itself a reaction to China’s development of the Pakistani Port of Gwadar). All is related; nothing in isolation.
But while it might seem, at least to the grinning faces in the Cabinet Room, that CAATSA represents a trump card (so to speak), it is in reality an unimaginative approach without any sort of backup plan. Should sanctions fail, then what? Unfortunately, the US overreliance on sanctions – as well as an insistence on mirroring rather than proportionality – has begun to generate a global financial regime wholly independent of the United States.
Nothing says that sanctions beget sanctions, or that tariffs must be exchanged tit for tat. One needn’t respond with identical measures so long as the response is proportional, unless escalation is the goal. Consider the “side-principle” rule articulated in Unrestricted Warfare:
Other means…supplement, enrich, or even replace military means, so as to achieve objectives which cannot be achieved by military force alone. This has been the most important episode of the side element’s modifying the principal element in relation to war on the basis of a conception of war … The side-principal rule is opposed to all forms of parallel placement, balance, symmetry, being all-encompassing, and smoothness, but, instead, advocates using the sword to cut the side. Only by avoiding frontal collisions, will it be possible for your sword to cut apart things without being damaged. This is the most basic grammar of victory for the ancient article of war [emphasis mine].
For instance, in reference to the ongoing trade war, Dean Baker has done an ample job illustrating that China could do far worse than simply retaliate with their own tariffs: US corporations stand to lose tens if not hundreds billions of dollars of intellectual property if the CCP were to opt out of enforcing copyright law. (Indeed, some version of this has already begun, albeit incidentally, as a thriving Chinese market in imitation/”homage” goods goes unchecked.)
Focusing on the trade war as a binary loses sight of the global picture, and as in so many other realms, the United States is no longer “indispensable” when it comes to international finance, either.
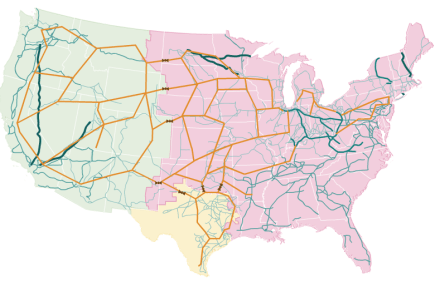
Indeed, on 25 September, the foreign ministers of Russia, China, Germany, France, and the UK (the latter three representing the EU) issued a joint statement committing them to continued adherence to JCPOA, and more importantly, to establishing a “special purpose vehicle,” a separate payments system to allow them to process transactions without touching US financial institutions. The SPV, according to Federica Mogherini, would “allow European companies to trade with Iran in accordance with EU law and could be open to other partners in the world.” Essentially, the SPV is a new means of subverting US sanctions on a multilateral basis, and should it prove successful in allowing the EU (and possibly India) to continue supporting the JCPOA and doing business with Iranian companies, could portend a future of decreasingly effective unilateral sanctions.
The rise of economic sanctions has been well-traced, and in the era of imperial presidencies, have been an easy way for Congress to reinsert itself at least somewhat into foreign policy-making. But the ensuing American way of war – airpower, special operations forces, and sanctions – has not been a productive one. Overreliance on sanctions leading to the development of a US-less financial system would be an own goal, indeed. Coupled with the rise of other shadow economies, like cryptocurrencies, dark pool trading, and alternative international settlement mechanisms (not to mention the already-challenging problem of nested shell corporations and beneficial owners), unilateral sanctions will continue to lose their effectiveness as targets increasingly find ways around them.
As Peter Harrell and Elizabeth Rosenberg argued in Foreign Policy earlier this year, “the reckless use of U.S. sanctions could speed the migration of China, Russia, and other U.S. adversaries away from U.S. markets and currency. The Trump administration needs a major new effort to understand and adapt to potential risks that threaten to reduce the power of U.S. sanctions.” No such effort was undertaken. And the migration has indeed sped up.
US grand strategy in the twenty-first century has been almost entirely counterproductive. Adversaries like Russia and China were likely to pursue alternatives to the US-dominated financial system at some point, but by multilateralizing opposition to that system (and ensuring that even our allies want an alternative) we have made our position more tenuous even sooner. The seeds the foreign policy establishment has planted over the past few decades are starting to fruit, and we will find the taste not at all to our liking.